OpenCPO Core
OCPP 1.6 + 2.0.1 Central System with zero trust networking baked in. Profile-driven charger compatibility handles the real-world firmware quirks that break other implementations.
View repoThe only EV charging platform
where chargers are invisible on the internet.
Enterprise-grade security. Open source. No compromise.
Zero trust networking, built-in PKI, and ISO 15118 Plug & Charge —
built by an actual CPO running real chargers.
Includes a complete guide to becoming a CPO with minimal cost —
from installation to Plug & Charge, OCPI roaming, and EU subsidies.
The Reality
Most commercial CPO platforms share the same fundamental architecture. And it's broken.
Chargers communicate directly over the public internet. No VPN. No tunnel. Anyone can scan for your endpoints and probe your infrastructure.
Entire networks secured by a single shared OCPP password. One leak — one disgruntled employee, one phishing email — and every charger on your network is compromised.
The server has no way to verify that a charger connecting is actually your charger. Rogue devices can impersonate legitimate hardware.
Many deployments use plain WebSocket without TLS. Charging commands, session data, energy readings — all readable by anyone on the path.
Man-in-the-middle attacks. Replay attacks. Unauthorized remote control of chargers. The attack surface is wide open.
The EU's NIS2 directive requires encrypted communications, identity verification, and audit trails for critical infrastructure. Most platforms aren't close.
The Differentiator
OpenCPO doesn't patch the broken model. It replaces it entirely.
Designed for deployment over WireGuard mesh VPN (e.g. Tailscale). A lightweight gateway — a Raspberry Pi at each site — bridges chargers into the private mesh. No public endpoints. No open ports. Chargers are invisible on the internet.
Own Root CA, CPO Sub-CA, MO Sub-CA. Every device gets a unique digital certificate — its own passport. No shared passwords. Revoke access in under one second.
Both sides verify identity. The charger proves it's your charger. The server proves it's your server. Every single connection, every time. Zero implicit trust.
Full PKI hierarchy for ISO 15118: Root CA, CPO Sub-CA, MO Sub-CA. SECC cert signing and contract cert provisioning handlers built into the OCPP 2.0.1 stack. The foundation for app-less, card-less charging.
Encrypted communications, verified device identity, audit logging. OpenCPO is designed with the EU's critical infrastructure directive in mind — so you're building on the right foundation from day one.
Every command, every session, every authentication event — logged and queryable. Who authorized what, when, and from which verified device. Built for forensics and compliance reporting.
What You Get
Six purpose-built components. One platform. No missing pieces, no "build the rest yourself."
OCPP 1.6 + 2.0.1 Central System with zero trust networking baked in. Profile-driven charger compatibility handles the real-world firmware quirks that break other implementations.
View repoNetwork management dashboard — chargers, sessions, tariffs, PKI management, and a live OCPP message viewer. Full visibility into your infrastructure.
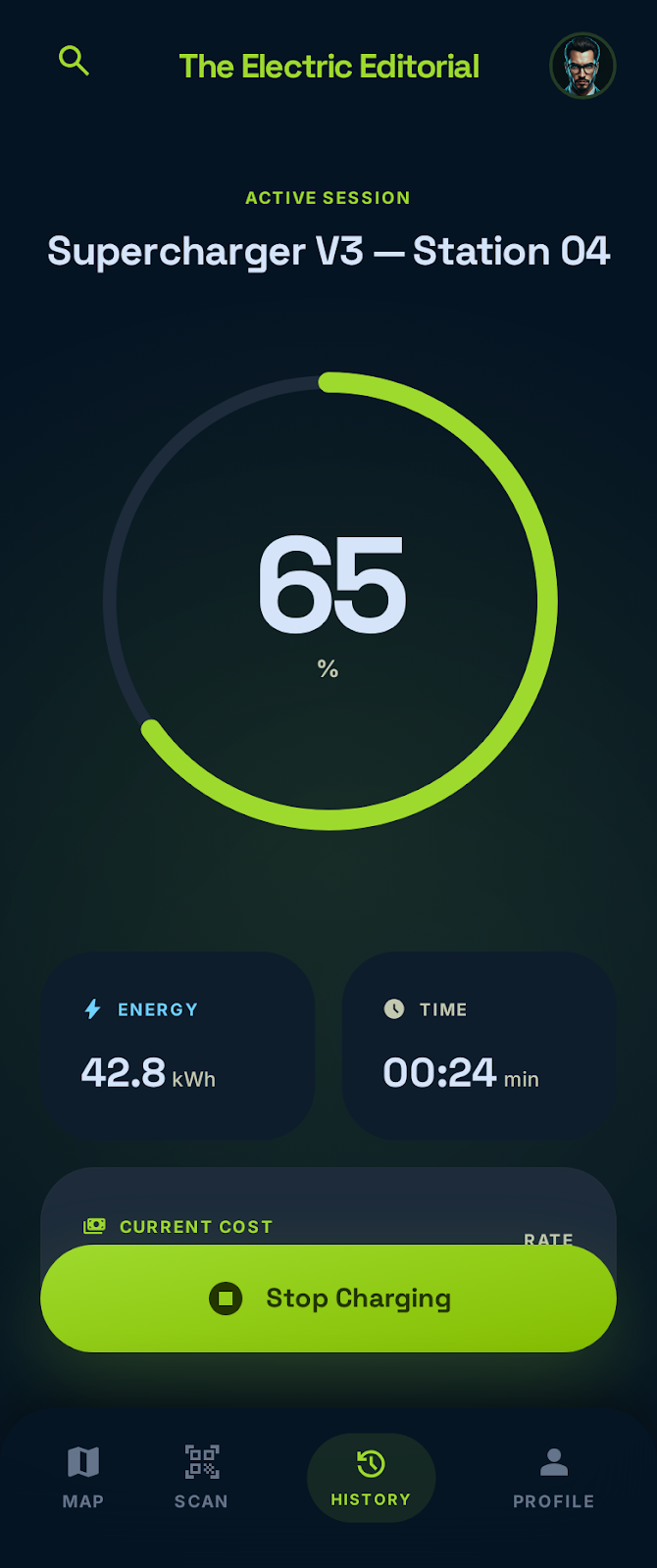
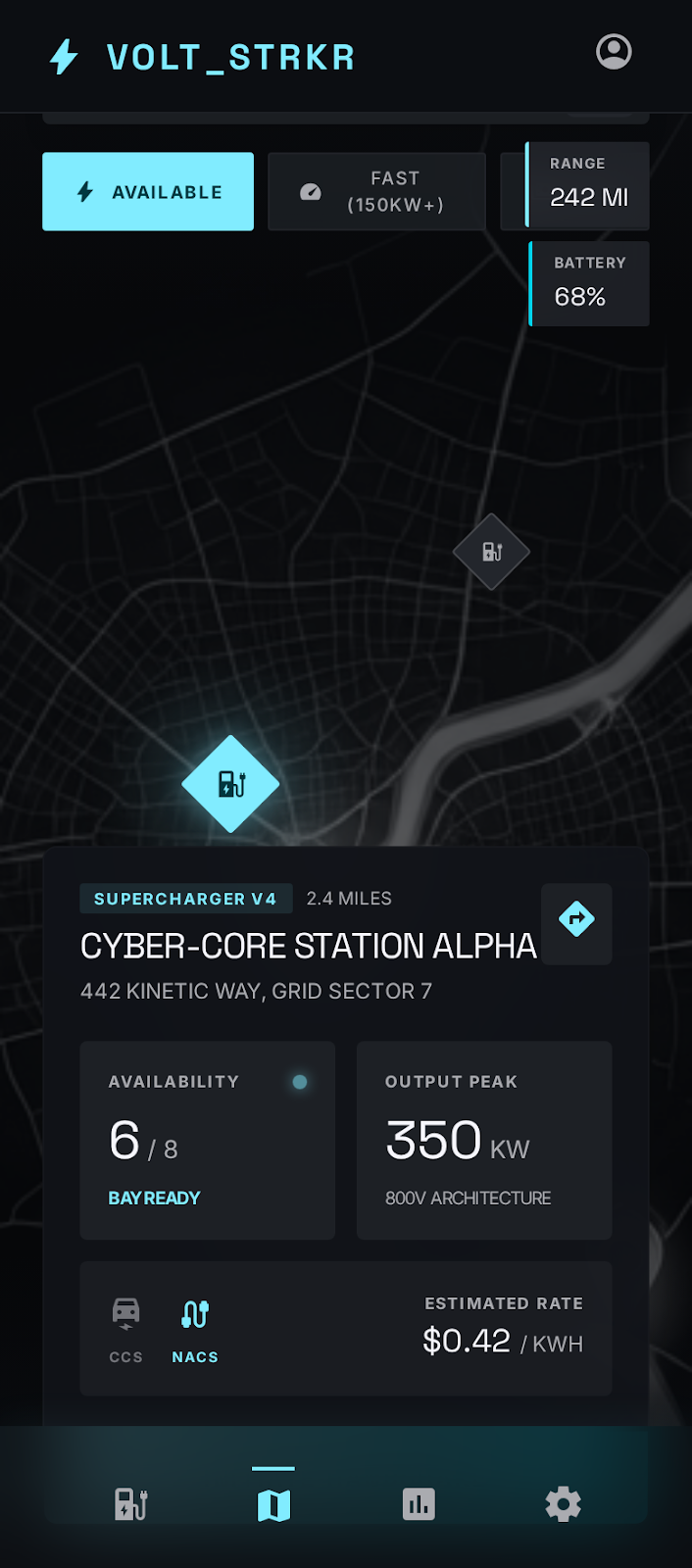
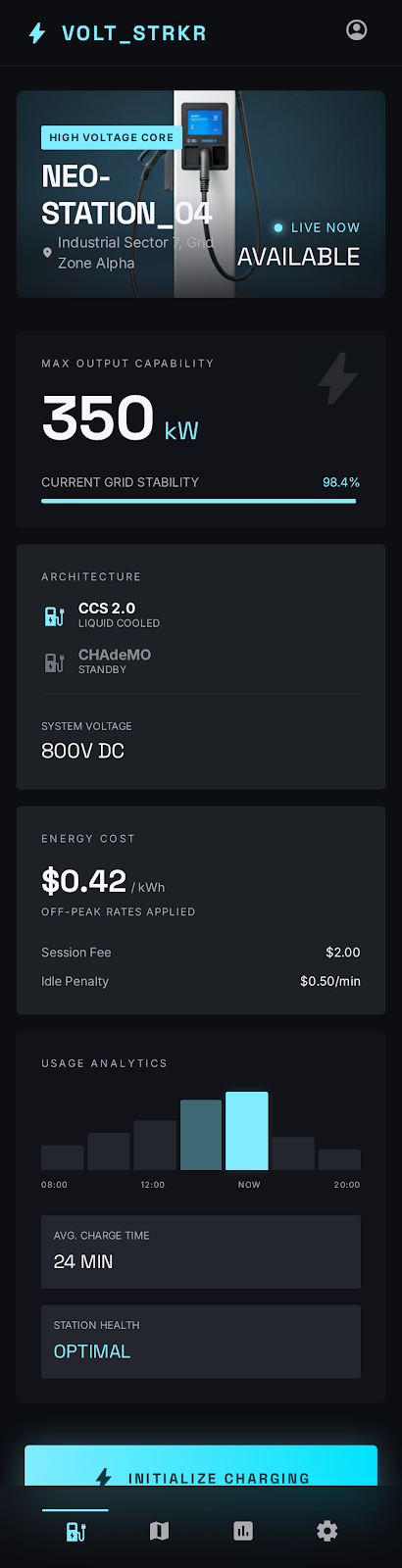
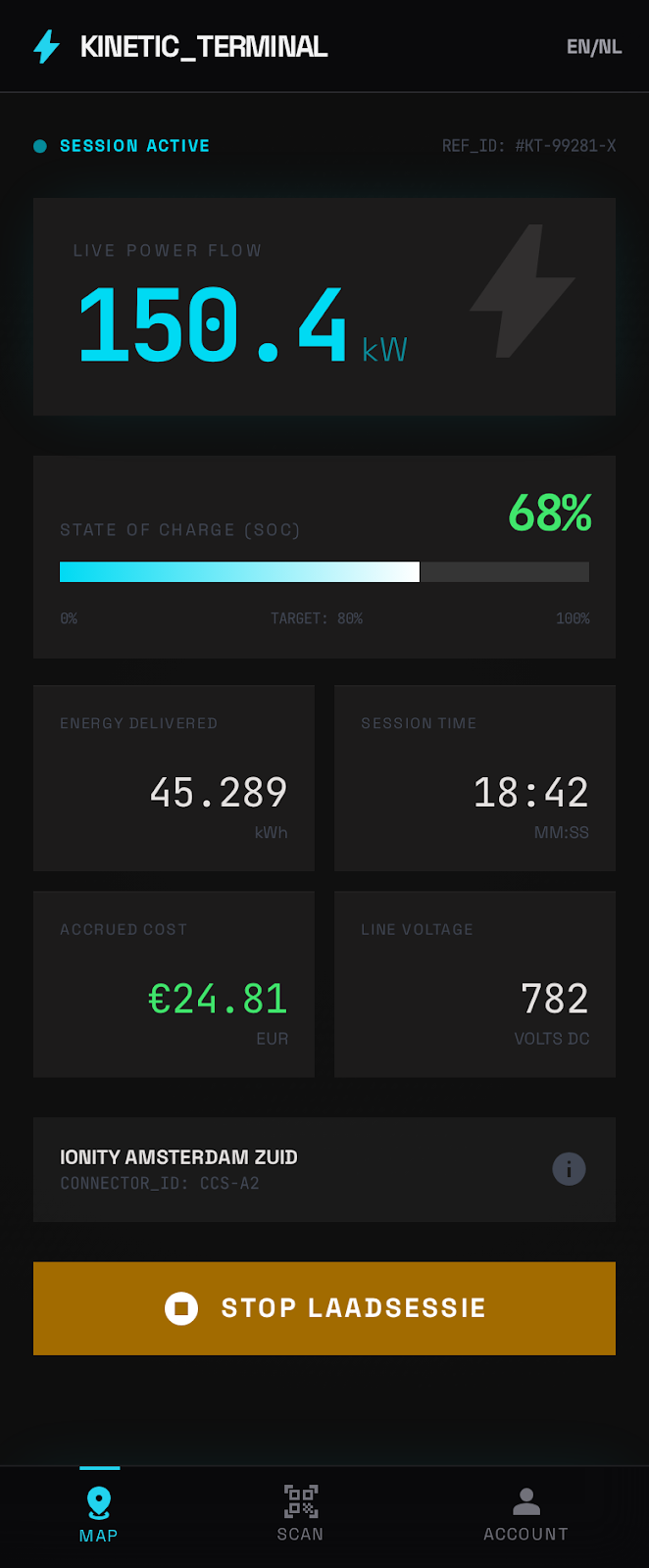
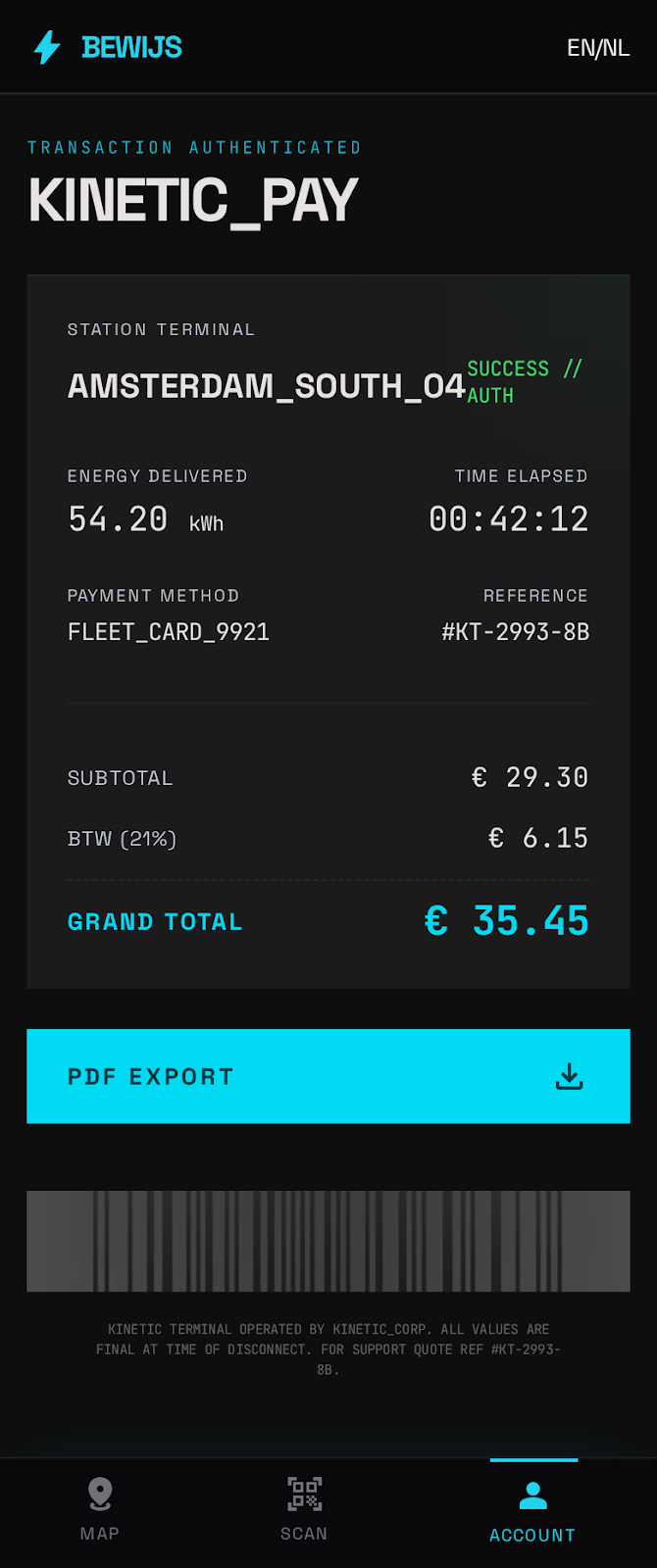
View repoDriver-facing PWA — scan QR, charge, pay. No app store needed. Works on any device with a browser.
View repoVirtual charger simulator with 18 stress test scenarios. Simulate entire networks without hardware. Load test before you deploy.
View repoFlashable site controller for Raspberry Pi or NanoPi. Zero-trust bridge, OCPP proxy, cert vault, sensor array, UniFi camera integration, LPR, 4G failover — with optional HA pair for zero-downtime sites.
View repoOCPP compliance test suite — validate your charger firmware against the spec before deploying. Structured test reports with pass/fail per message type.
View repoWhite-Label Ready
One engine, infinite looks. Switch skins with a single environment variable — or create your own in minutes using Google Stitch.
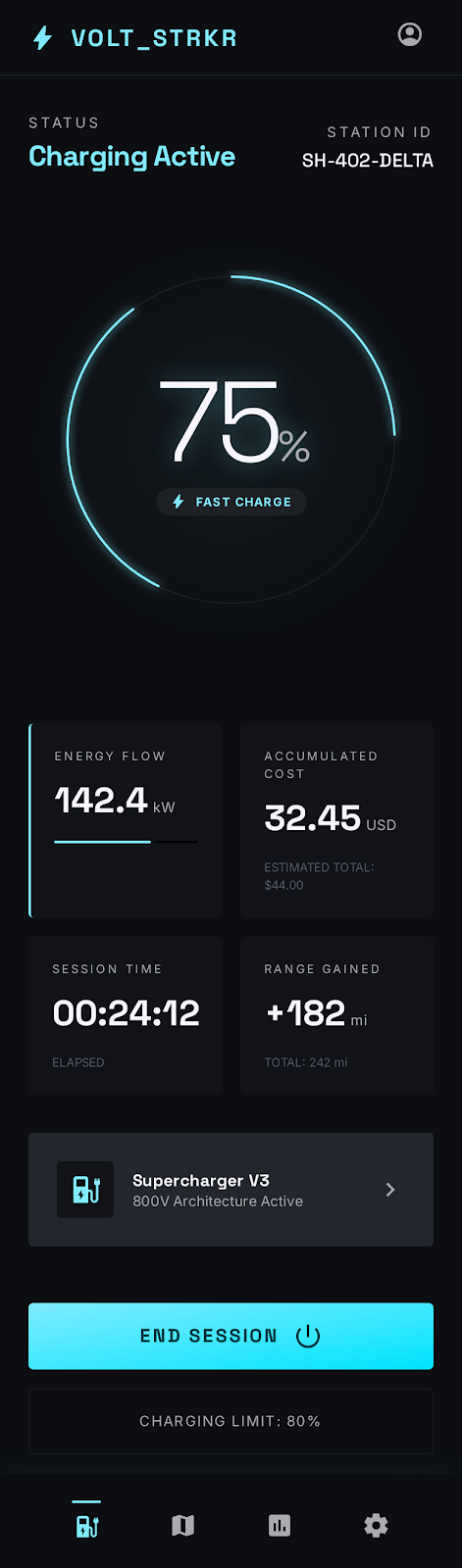
Theater control room aesthetic — stage lighting glows, atmospheric depth




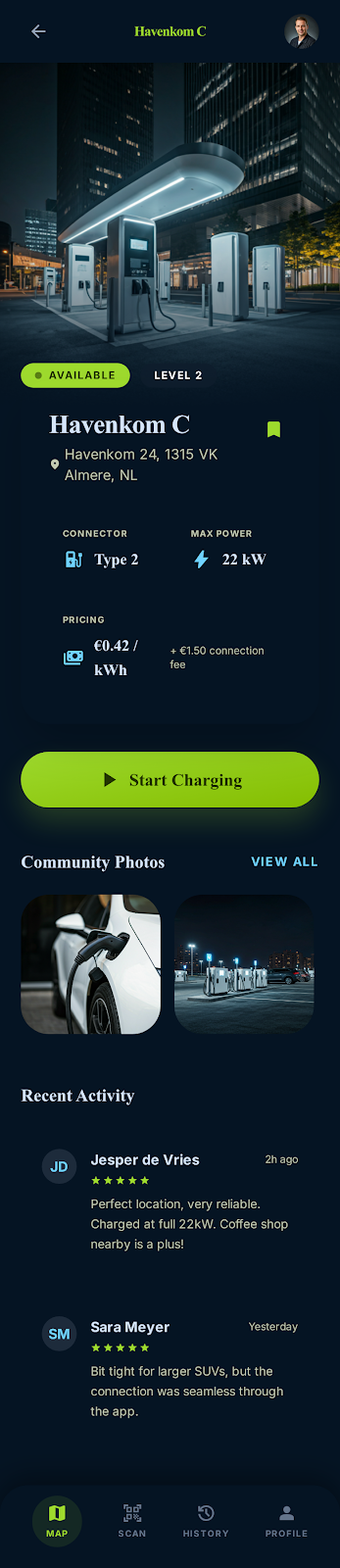
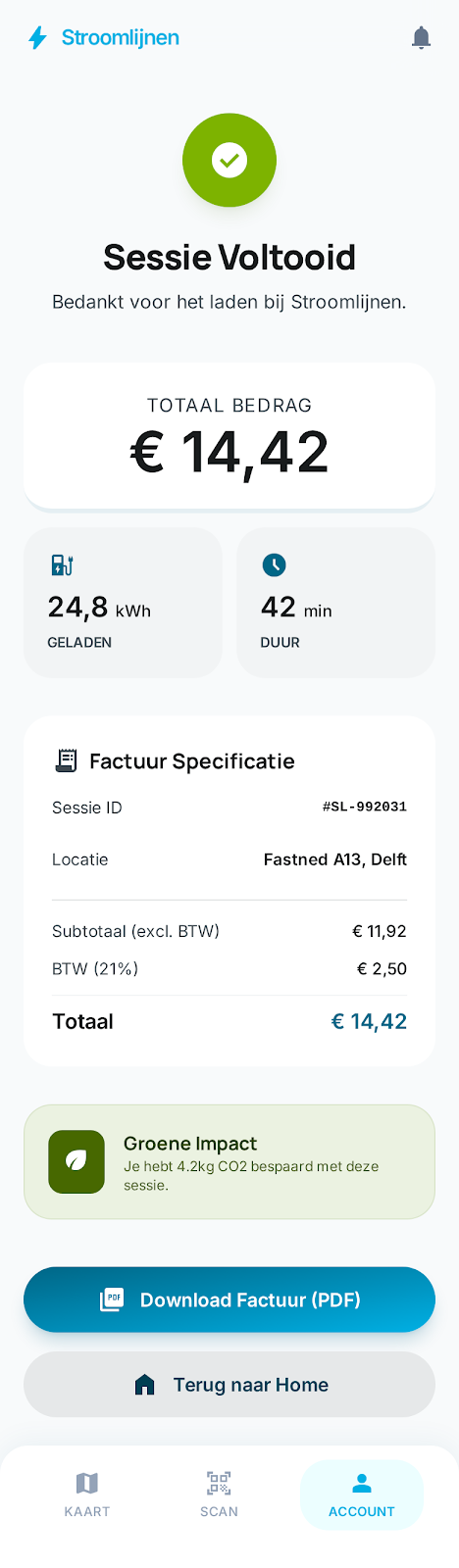
Editorial lifestyle — lime green energy, community-driven feel

Obsidian HUD — carbon fiber depth, neon cyan data strikes
Clean Dutch editorial — sunlight-readable, eco-conscious


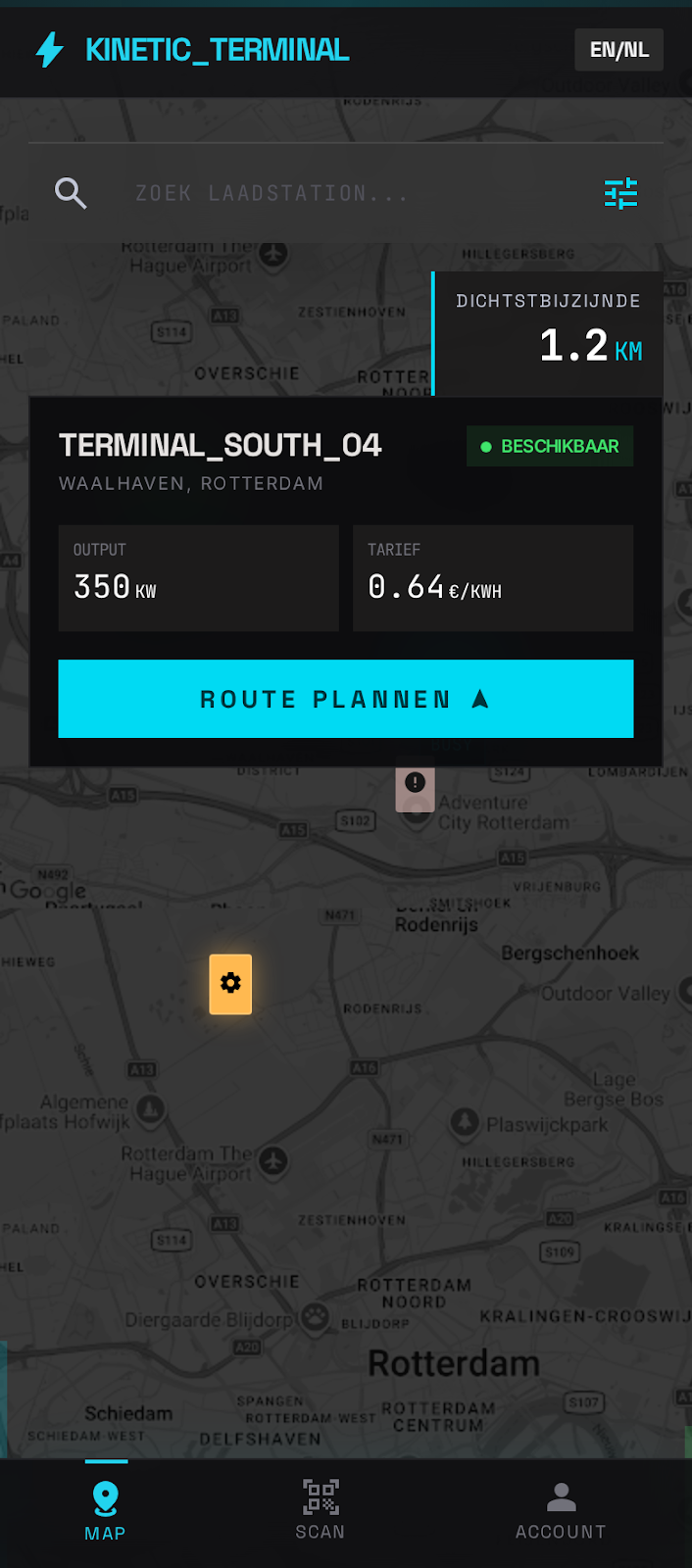
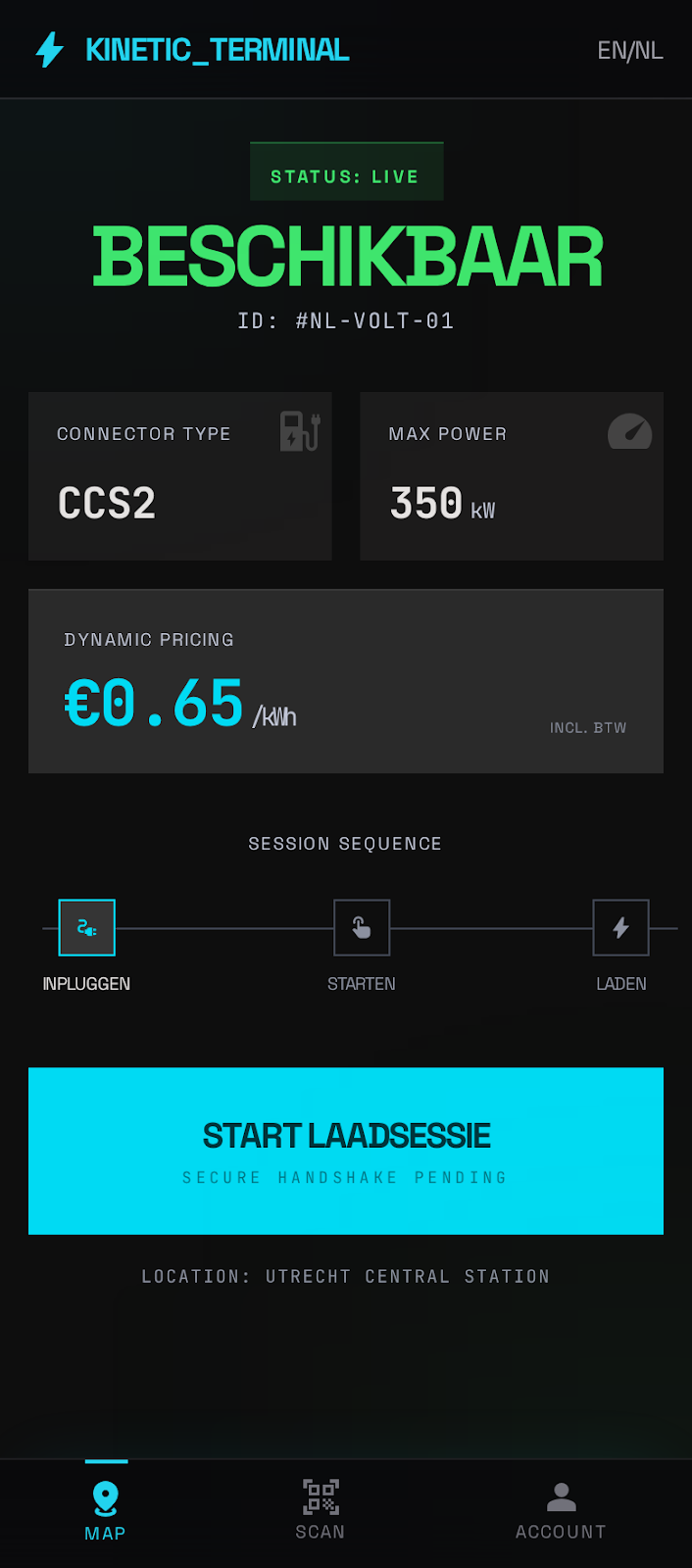
SCADA terminal — monospace readouts, industrial HMI precision
stitch-to-skin → deploy. Your brand, your colors, your typography — on top of the same rock-solid charging engine.
How We Compare
One platform checks every box. Most are starting from scratch.
| Feature | OpenCPO | Commercial Platforms (typical) | ||
|---|---|---|---|---|
| Zero trust networking | ✓ | ✗ | ||
| Built-in PKI & mTLS | ✓ | ✗ | ||
| ISO 15118 Plug & Charge | ✓ | ~ | ||
| Open source | ✓ | ✗ | ||
| Self-hosted / no vendor lock-in | ✓ | ✗ | ||
| NIS2-aligned by design | ✓ | ~ | ||
| Skinnable driver app | ✓ | ✗ | ||
| €0 license cost | ✓ | ✗ | ||
~ = Partial or limited support. Based on publicly available documentation as of 2026.
Why This Matters
OpenCPO isn't just a better platform. It changes what's possible for the industry.
Building a PKI, mTLS, and zero trust networking stack from scratch takes significant engineering investment. OpenCPO gives you that foundation for free. Small operators get the same security architecture as enterprise players.
Write "OpenCPO" into procurement specs. Full source visibility means no black-box surprises. No vendor lock-in means you own your infrastructure — not a SaaS provider.
Every friction point removed — cost, complexity, security — means more operators entering the market. More operators means more chargers. More chargers means faster EV adoption. The math is simple.
Every security improvement in OpenCPO benefits every installation running it. Community contributions raise the baseline for everyone. The Red Hat model: the software is free — the expertise is the product.
Quick Start
No complex setup. No configuration maze. Clone, setup, compose.
For production, connect chargers via Tailscale — every device gets a WireGuard identity and joins your private mesh automatically. No public endpoints needed. See the deployment guide for Tailscale integration and certificate provisioning.
Credibility
OpenCPO is production code from a team that charges real vehicles every day. Not a consultancy slide deck. Not a university project. Not a proof of concept.
We run our own CPO network — real chargers, real drivers, real revenue. Every feature in OpenCPO was built because we needed it ourselves. Every edge case was encountered in production and fixed in the codebase.
The software is free. The expertise is the product.
We built the security infrastructure every CPO needs. Now we're sharing it with the industry — and offering the expertise to deploy it right.
Community
OpenCPO gets better when the whole industry contributes. Join us.
Real-time chat. Get help, share what you're building, join discussions about OCPP, security, and EV charging.
Long-form conversations, feature requests, RFC proposals, and Q&A — all tracked in the open.
Bug fixes, new charger profiles, security improvements, protocol support. Every contribution raises the bar for everyone. See CONTRIBUTING.md.
Community database of charger behavior profiles. Running a vendor's hardware? Test it, generate a profile, submit a PR. Your fix helps every CPO using that charger.
Apache 2.0 license. No premium tier. No feature flags behind a paywall. Everything in the open source release.
Found a vulnerability? We take security seriously. Responsible disclosure process via SECURITY.md. Security fixes are prioritized above all else.
Everything you need to become a Charge Point Operator — from your first charger to multi-site OCPI roaming with Plug & Charge. Technical deep dives, deployment architecture, EU subsidies, and business model guidance. Free with demo access.
Covers OCPP 1.6j + 2.0.1 · ISO 15118 PKI · OCPI 2.2.1 roaming · multi-node HA deployment · financial incentives across 10 EU countries
Get access to a live demo environment with 20 simulated chargers running real OCPP sessions. Full admin dashboard, driver app, charger farm, API, and the complete CPO handbook — yours to explore.
Want to read first? Read the full CPO guide — installation, pricing, PKI, OCPI roaming, and EU subsidies.
Or email us directly at [email protected]